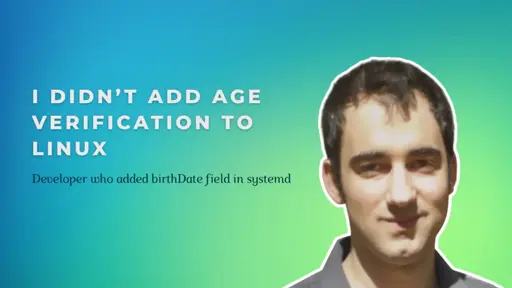
Dylan M. Taylor is not a household name in the Linux world. At least, he wasn’t until recently.
The software engineer and longtime open source contributor has quietly built a respectable track record over the years: writing Python code for the Arch Linux installer, maintaining packages for NixOS, and contributing CI/CD pipelines to various FOSS projects.
But a recent change he made to systemd has pushed him into the spotlight, along with a wave of intense debate.
At the center of the controversy is a seemingly simple addition Dylan made: an optional birthDate field in systemd’s user database.


This is stupid. We block fingerprinting.
Just because some people are fingerprint able doesn’t mean all of us should suffer and bend at the knee to unjust laws
You can’t really “block” fingerprinting. You can obfuscate it a bit, but the fingerprinting process happens server side, not on your device. So whether or not your system sends whatever age verification signal becomes a part of its fingerprint.
It’s not just server-side: A lot of fingerprinting happens client-side, for example using a canvas to check what features your graphics card supports. You can see this in action via services like https://coveryourtracks.eff.org/ or https://amiunique.org/
That’s not the fingerprinting happening client side, that’s just information supply. Fingerprinting is about what the server does with that information.
Yeah, but the countermeasures are client-side because that’s what you can control. And some kind FOSS devs out there make it easy to start somewhere decent.
Of course you can block fingerprinting. See Tor Browser. Everyone looks the same.
Or you can change your fingerprint every 30 seconds with a plugin like chameleon.
You know it works when evil sites all ban you because they can’t fingerprint you and track you between sessions anymore
That’s not blocking the fingerprinting, that obfuscating the data. The fact that you are doing that itself becomes part of the fingerprint being built. Services like Tor or Chameleon don’t stop the fingerprinting process running, they just make it more difficult (but not impossible) to tie the fingerprint to your actual identity.
It’s making the fingerprinting efforts useless. Sure, they can do it, but many of us are blocking them from being able to uniquely fingerprint and track us across the internet
deleted by creator
It’s not stupid insofar that it is an additional fingerprintable data point. But it’s obviously still much harder to fingerprint you if many users share the same value that you have, so it is invalid.